MISP Plugin for Threat Exchange
This document explains how to configure the MISP integration with the Threat Exchange module of the Netskope Cloud Exchange platform. This integration allows for sharing of URLs and file hashes with Netskope that has been identified by MISP or Netskope.
Misp is a threat intelligence platform for sharing, storing and correlating Indicators of Compromise of targeted attacks, threat intelligence, financial fraud information, vulnerability information or even counter-terrorism information. (More Info)
This plugin is used to fetch event attributes from MISP (Malware Information Sharing Platform) and extract indicators from them. It can also share the indicator Hash or URL to MISP Custom Event.
Fetched indicator types | MD5, SHA256, URL |
Shared indicator types | MD5, SHA256, URL |
Stack Size | Medium |
RAM | 16 GB |
Number of cores | 8 |
Pulling (~100K) IoCs from MISP | 10~ minutes |
Pushing (~100K) IoCs to MISP | 15~ minutes |
To complete this configuration, you need:
A Netskope Tenant (or multiple, for example, production and development/test instances).
Secure Web Gateway subscription for URL sharing.
A Netskope Threat Prevention subscription for malicious file hash sharing
A Netskope Cloud Exchange tenant with the Threat Exchange module already configured.
A MISP Instance.
Connectivity to the following host: http://10.50.2.106/
Get your MISP URL and API key.
Configure the MISP Plugin.
Configure sharing between Netskope and MISP.
Validate the MISP Plugin.
Click play to watch a video.
Your MISP Instance URL and API key are needed to later configure the MISP plugin in Threat Exchange.
Log in to your MISP Instance.
Copy your MISP Instance URL.
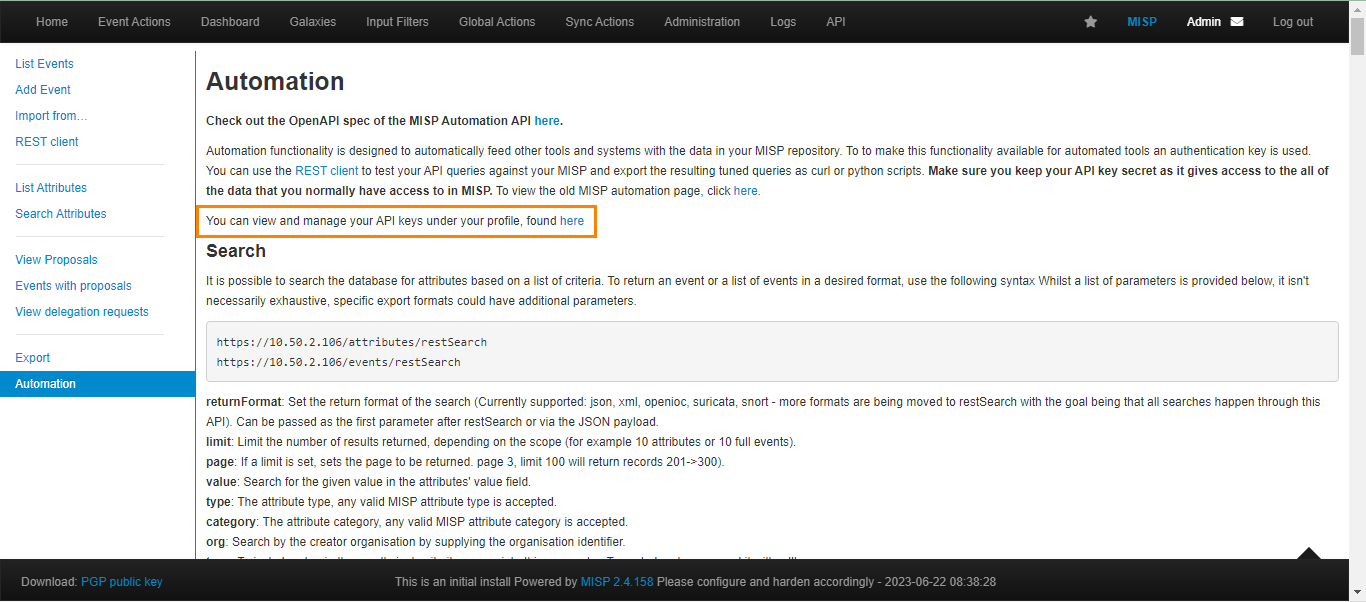
In the Home page left nav panel, click Automation.
Click on here in You can view and manage your API keys under your profile, found here.
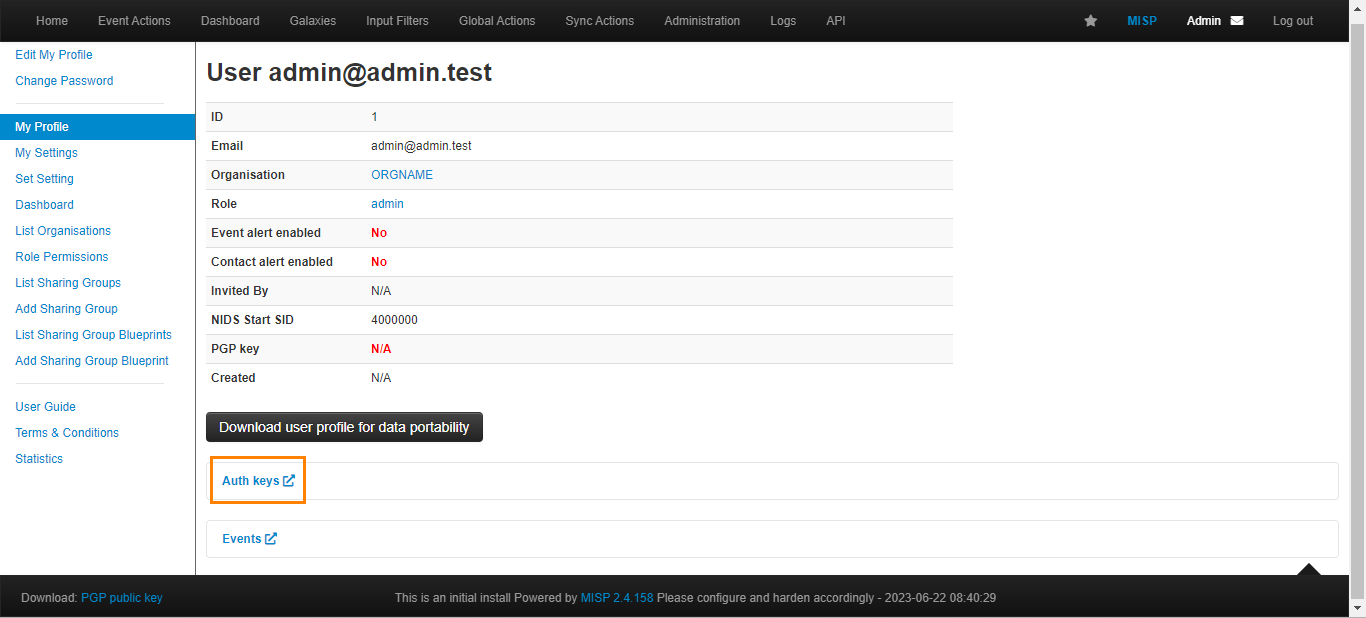
Click Auth keys.
Click Add authentication key.
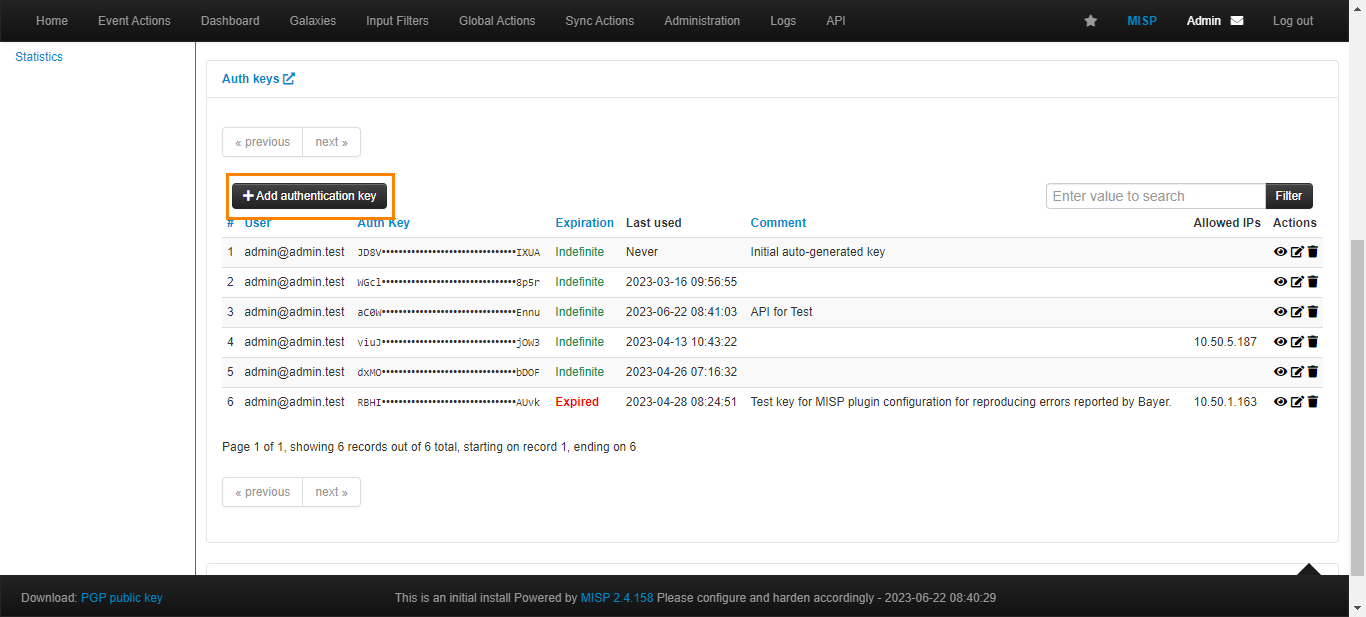
Your MISP API key will be shown here. Copy the API key to configure the MISP plugin.
In Cloud Exchange, go to Settings > Plugins.
Search for and select the MISP plugin box to open the plugin creation pages.

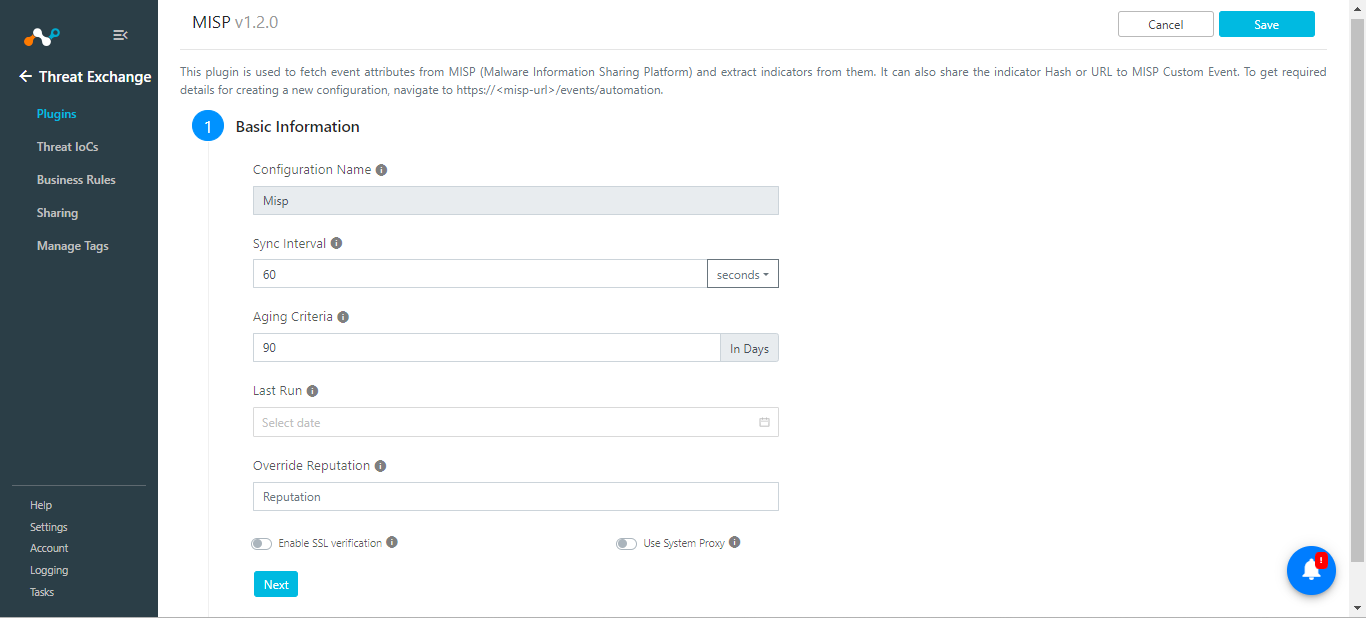
Enter the Basic Information on the first page:
Configuration Name: Enter a name appropriate for your integration.
Sync Interval: Adjust to environment needs. We recommend not to go below 5 minutes for production environments.
Aging Criteria: Enter the number in days.
Override Reputation: Adjust to the appropriate value.
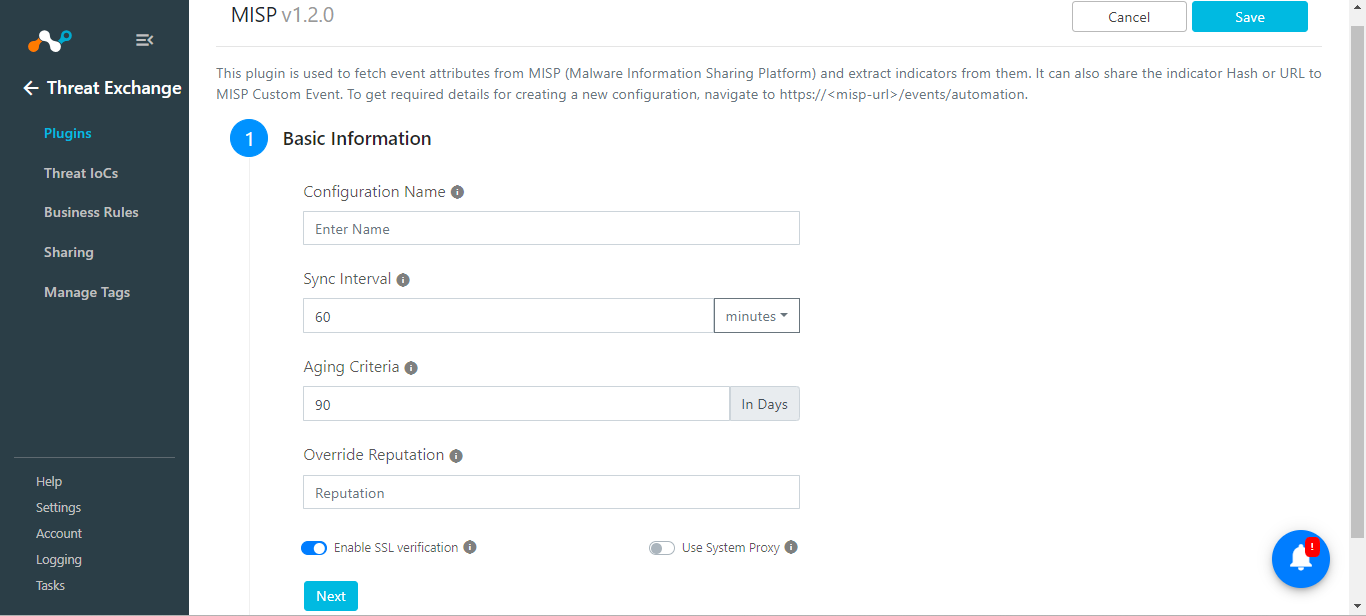
Click Next.
Enter the Configuration Parameters on the second page:
Base URL: Enter the URL of your MISP Instance.
API Token: Enter your MISP API key.
MISP Attribute Type: Options are SHA256, MD5, URL, DOMAIN, and IP. Indicators from only specified attribute types will be fetched. Keep empty to fetch indicators of all types. Multiple Types are accepted.
MISP Attribute Category: Indicators from only specified Attribute Categories will be fetched. Keep empty to fetch indicators of all Categories. Multiple Categories are accepted.
Enter MISP Attribute Tags: Indicators from only specified comma-separated Tags will be fetched. Keep empty to fetch indicators of all Tags. Dynamic values are accepted.
Event Name: Leave Event Names blank to fetch indicators from all the events, or enter them separately by comma to fetch only those indicators that belong to that event. For now, we leave it blank.
Exclude IoCs from Event: Enter the name of event(s) whose IoCs you want to exclude from being fetched.
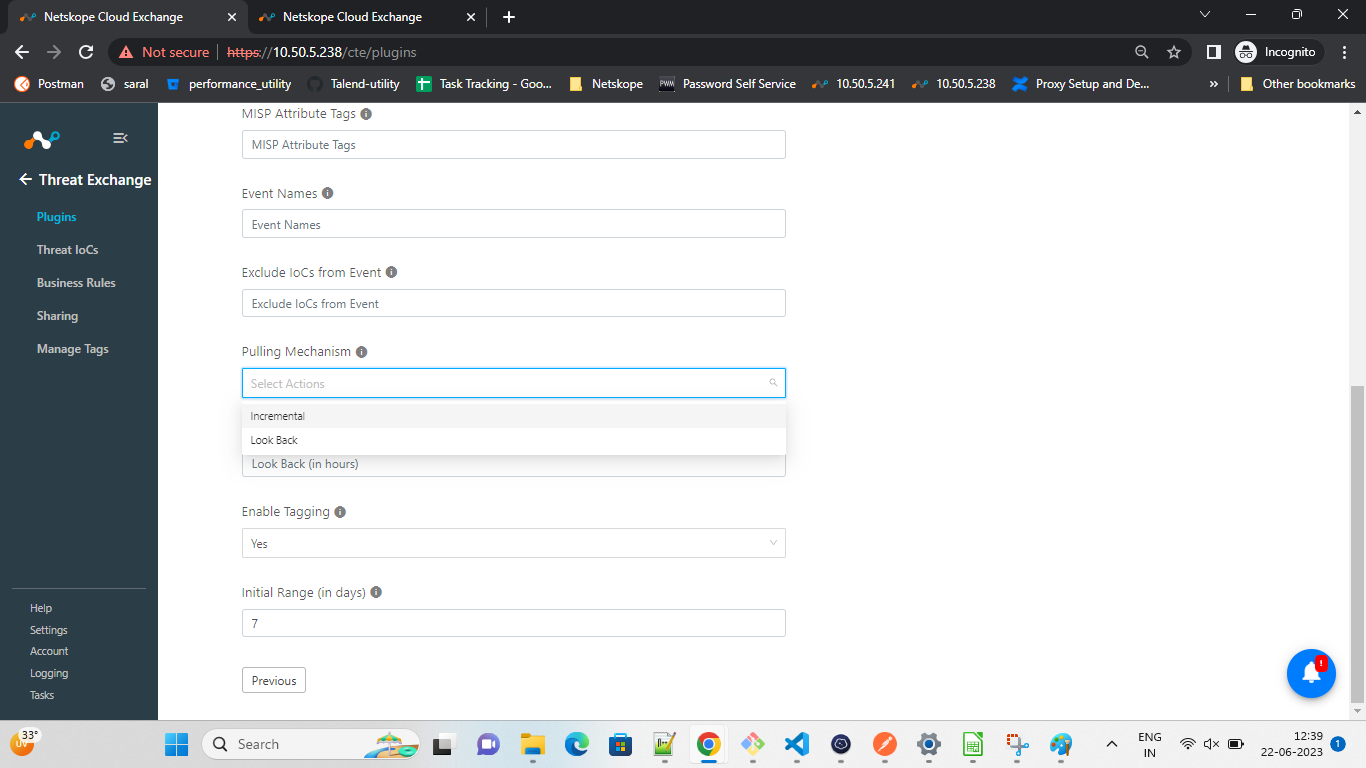
Pulling Mechanism: Select one of these options:
Incremental (Default): Plugin will fetch data using stored checkpoint, like
last_run_atof the plugin.Look Back: Plugin will fetch data subtracting lookback value from the plugin run time on every sync. For example, if provided value is 72 Hrs then it will fetch 72 Hrs of IOCs from now on every sync.
Enter Look Back (in hours) to pull the indicators of historical time from now on everytime the plugin syncs. Default value is set to empty and it will only be used when selected “Look Back” in Pullung Mechanism.
The rest of this form can remain as default.
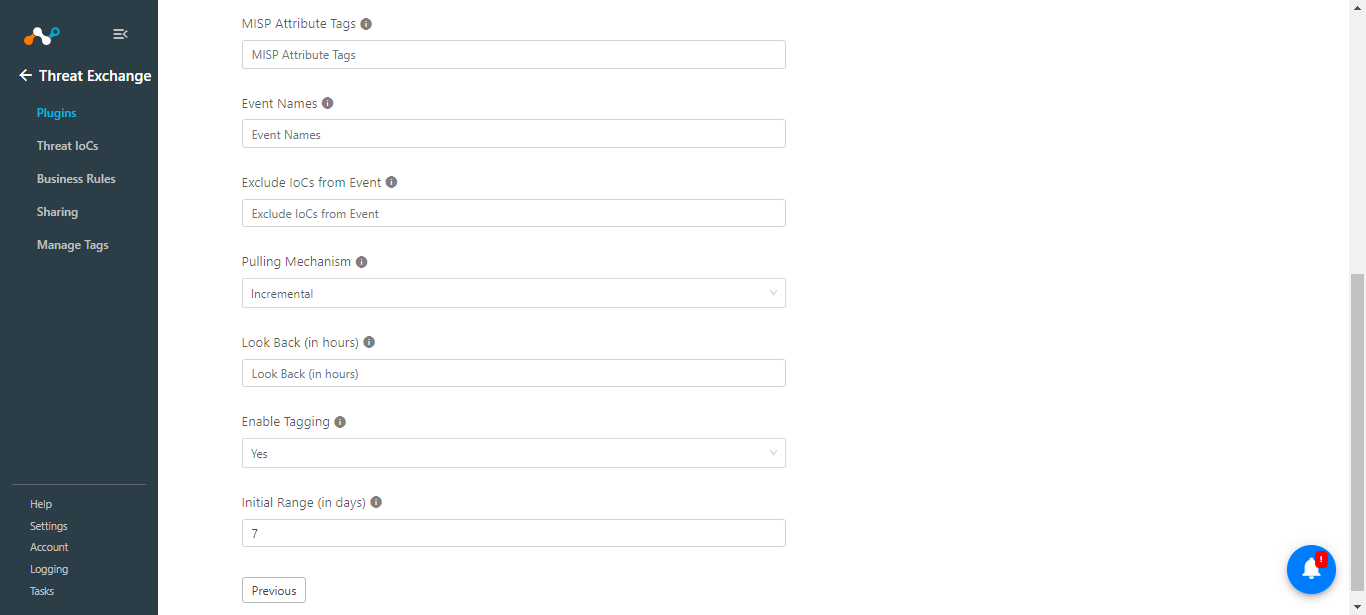
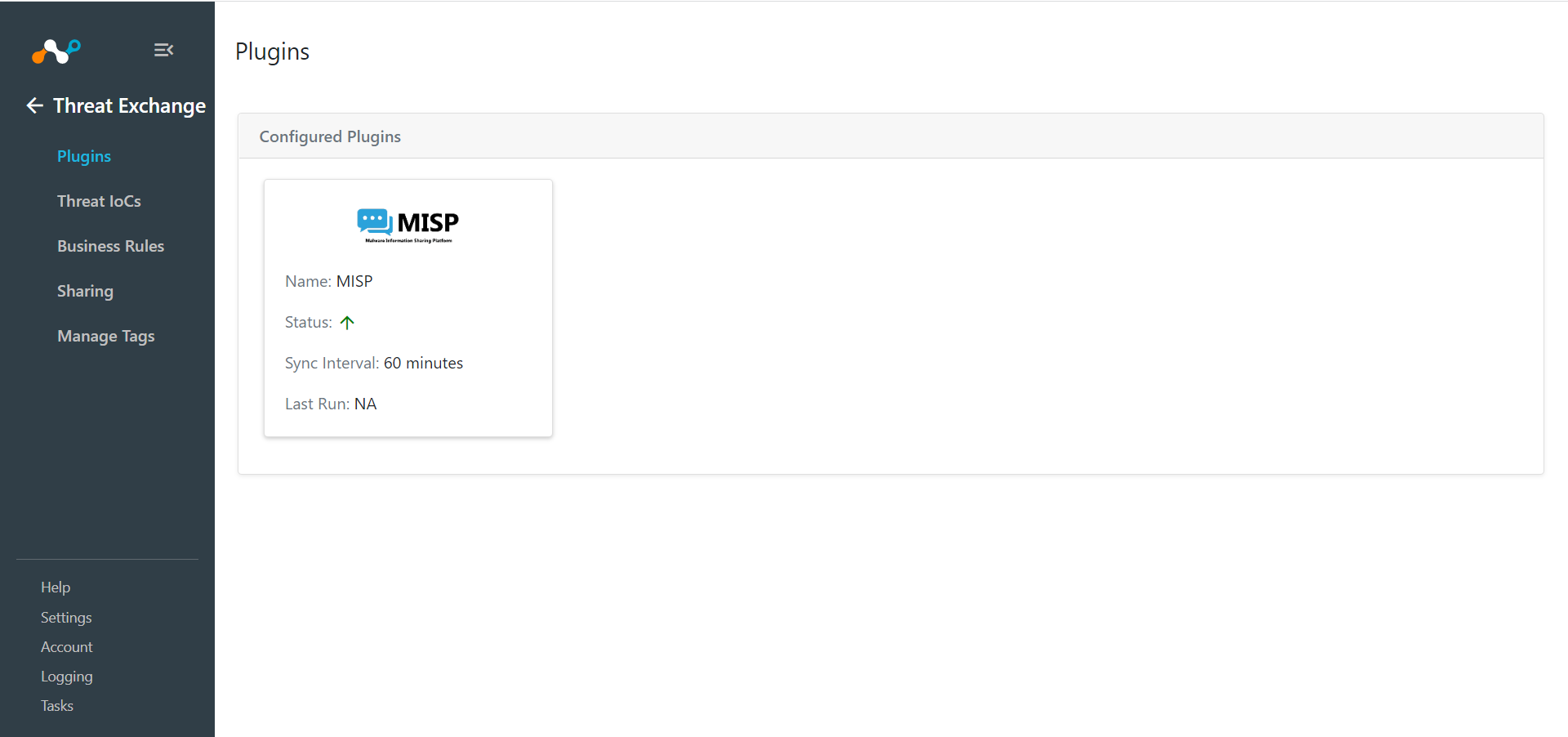
Click Save. You new plugin appears on the Threat Exchange > Plugins page.
Note
IoCs stored to Netskope Cloud Exchange will have current date and time as
Last_Seenrather than the MISP's last seen.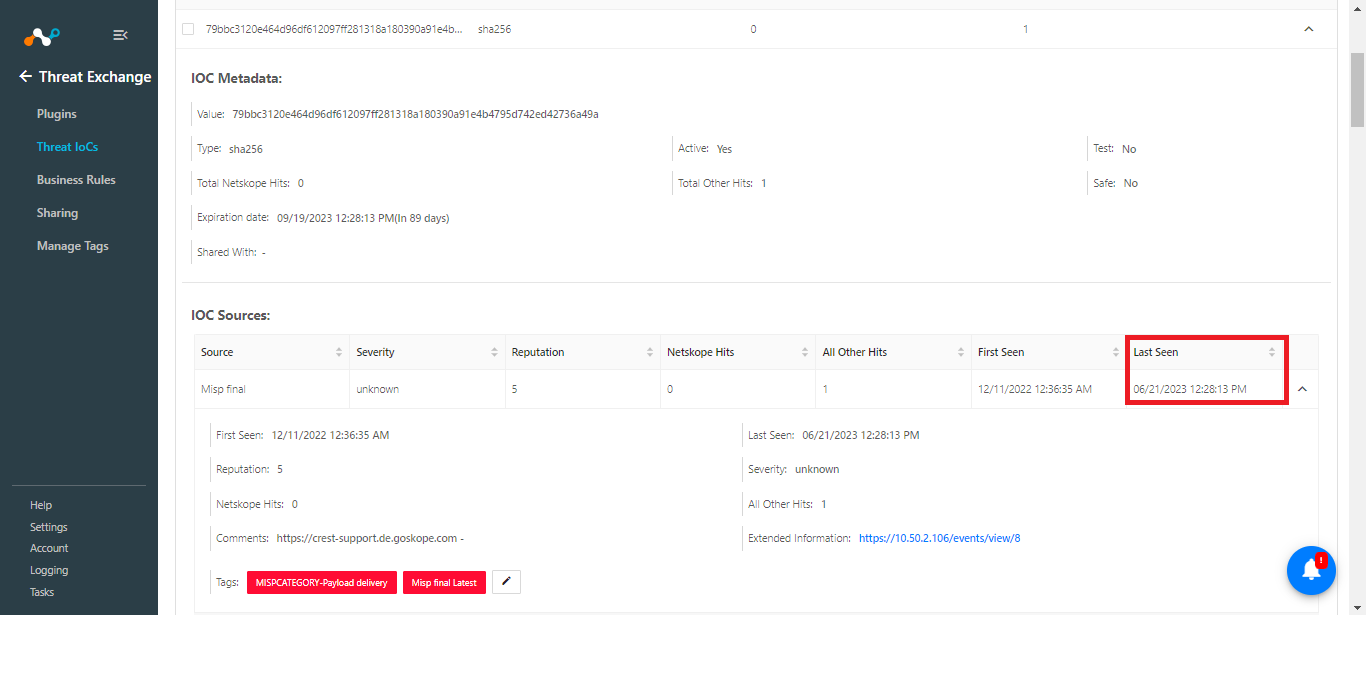
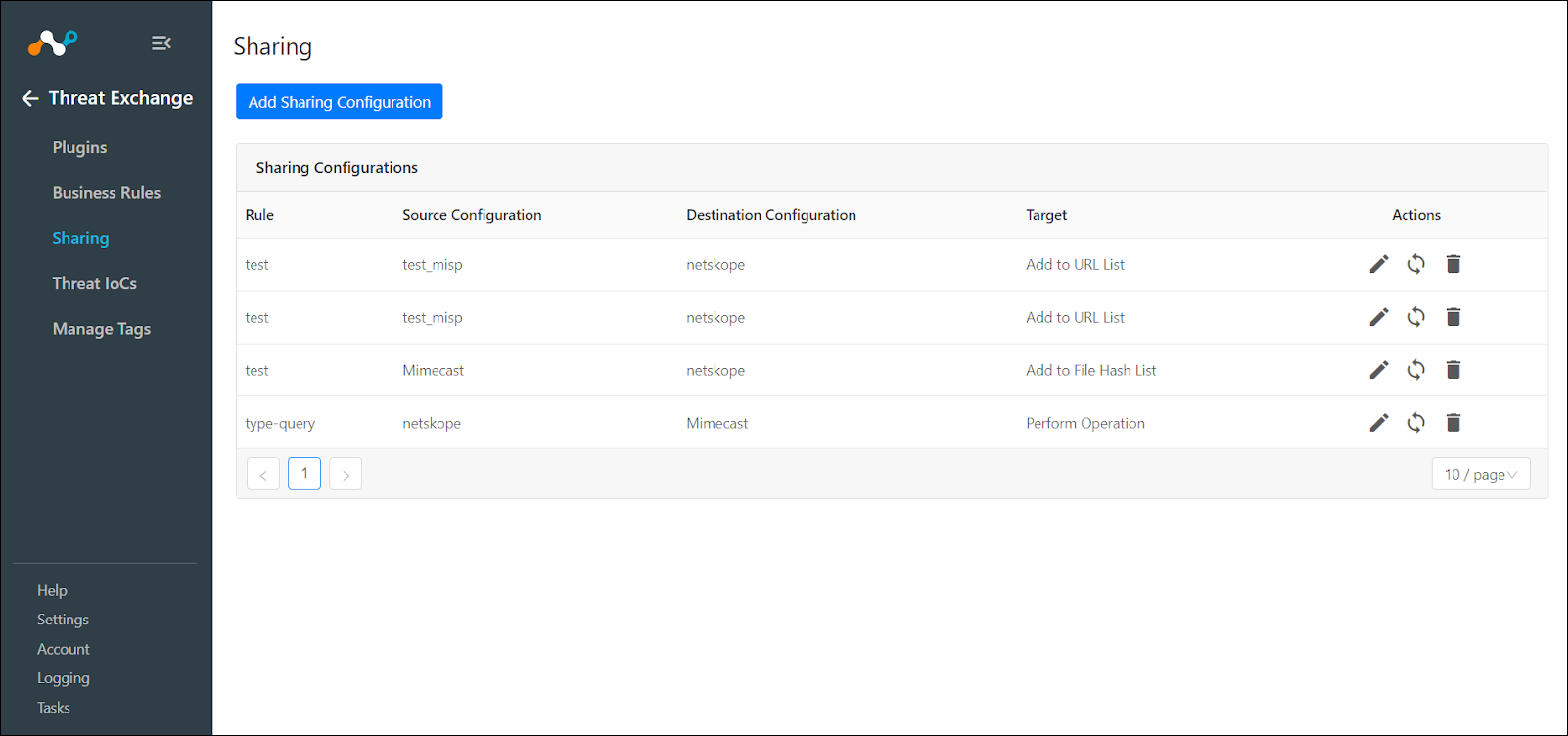
Go to Threat Exchange and select Sharing. The Sharing page displays the existing relationships for each sharing configuration in grid view as shown below. The Sharing page also has inputs to configure new sharing from one plugin to another.
Click Add Sharing Configuration, and in the Source Configuration dropdown list, select MISP.
Select a Business Rule, and then select Netskope for the Destination Configuration. Sharing configurations are unidirectional. data obtained from one plugin is shared with another plugin. To achieve bi- or multi-directional sharing, configure each separately.
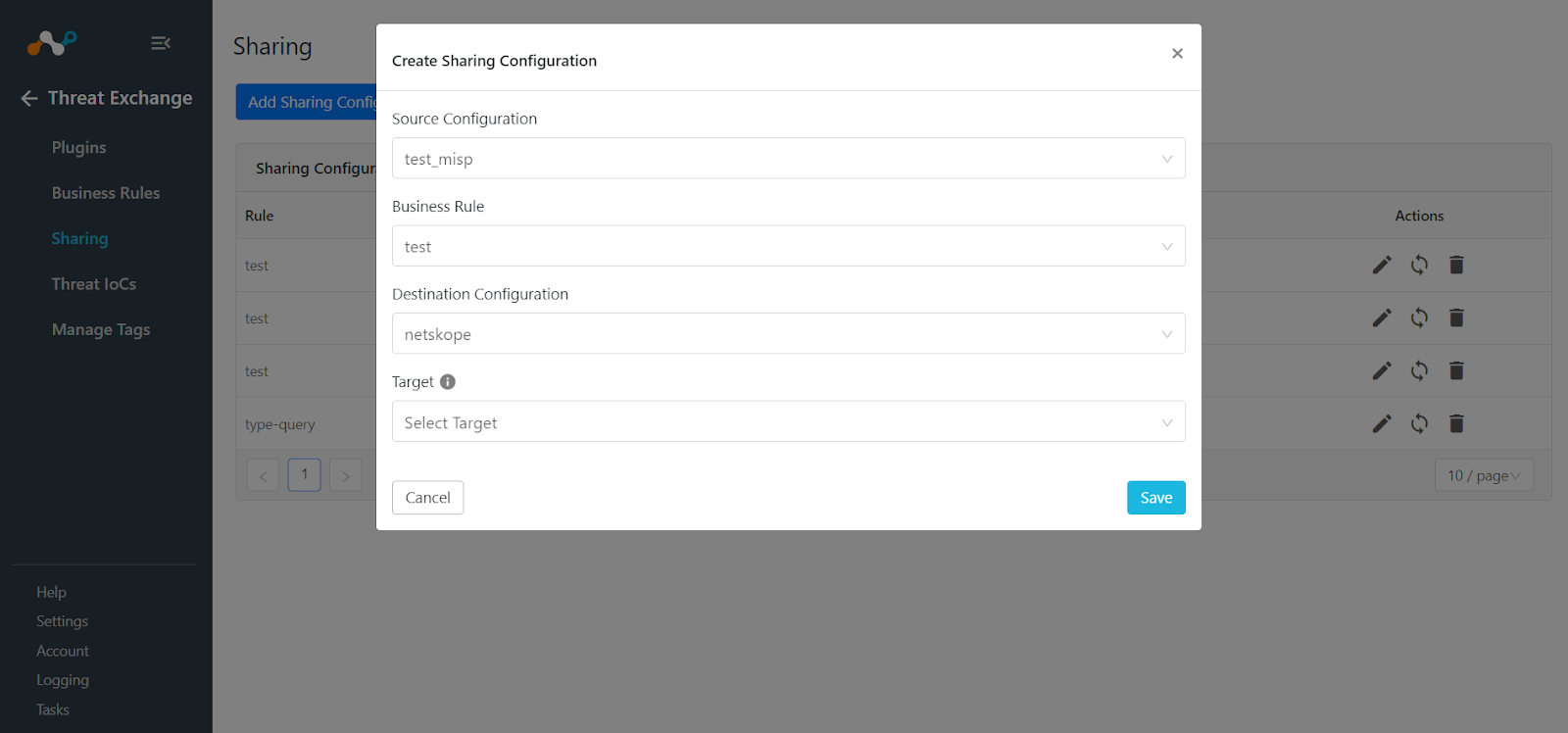
Select a Target. Each plugin will have a different target or destination for the IoC.
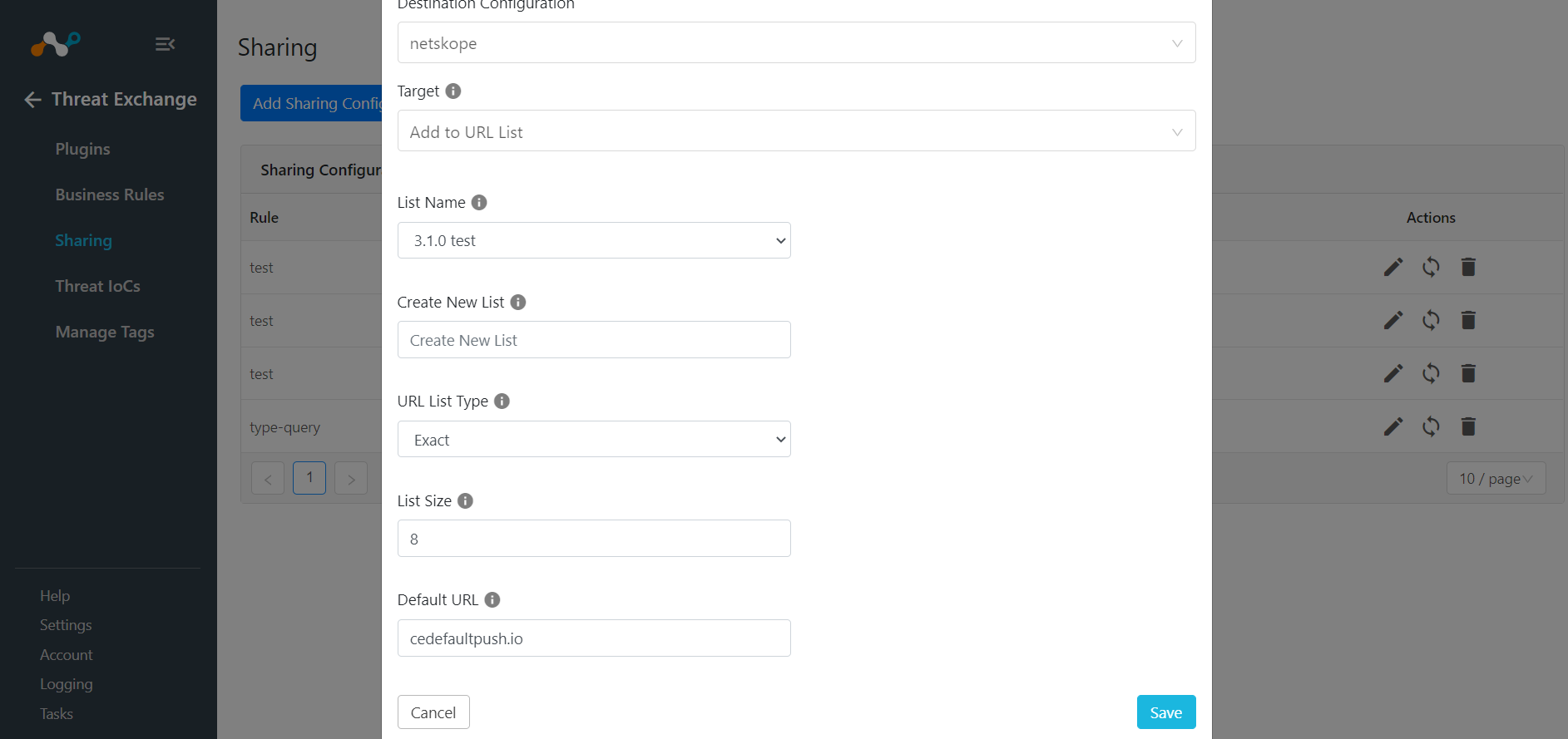
If you selected Add to URL List, follow these steps.
Select the List Name or select Create new list from the dropdown, and then enter a New List Name.
Click Add to URL List.
Enter a List Size.
Enter the Default URL.
Click Save.
If you selected Add to File Hash List, follow these steps.
Enter the List Name.
Enter a List Size.
Enter the Default File Hash.
Click Save.
Repeat steps 2-6, but select Netskope as the Source Configuration and MISP as the Destination Configuration.
Click Save.
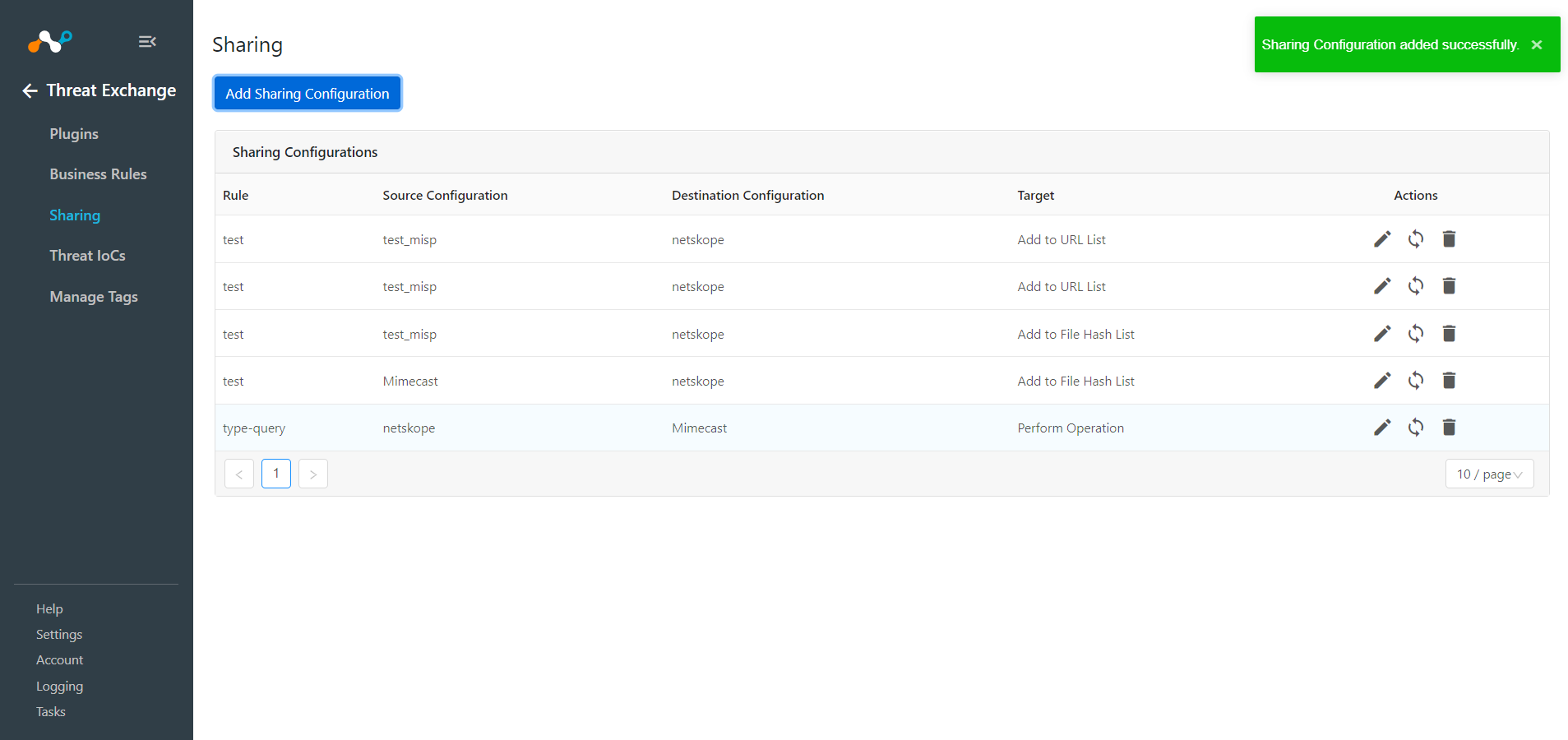
Adding a new sharing configuration on the active source poll will share the existing IoCs of the source configuration to the destination configuration. Whenever a new sharing configuration is built, all the active IoCs will also be considered for sharing if they match the source/destination combination.
Note
Plugins that do not have API for ingesting data cannot receive threat data. This is true of the installed plugin API Source, which provides a bucket associated with an API endpoint for remote 3rd-party systems to push data to. Once a Sharing policy has been added, it takes effect.
After a sharing configuration has been created, the sharing table will show the rule being invoked, the source system providing the potential IoC matches, the destination system that will receive matching IoC, and the target applicable to that rule. Multiple Sharing configurations can be made to support mapping certain IoC to multiple targets even on the system destination system.
Modify, Test, or Delete a Sharing Configuration
Each configuration supports 3 actions:
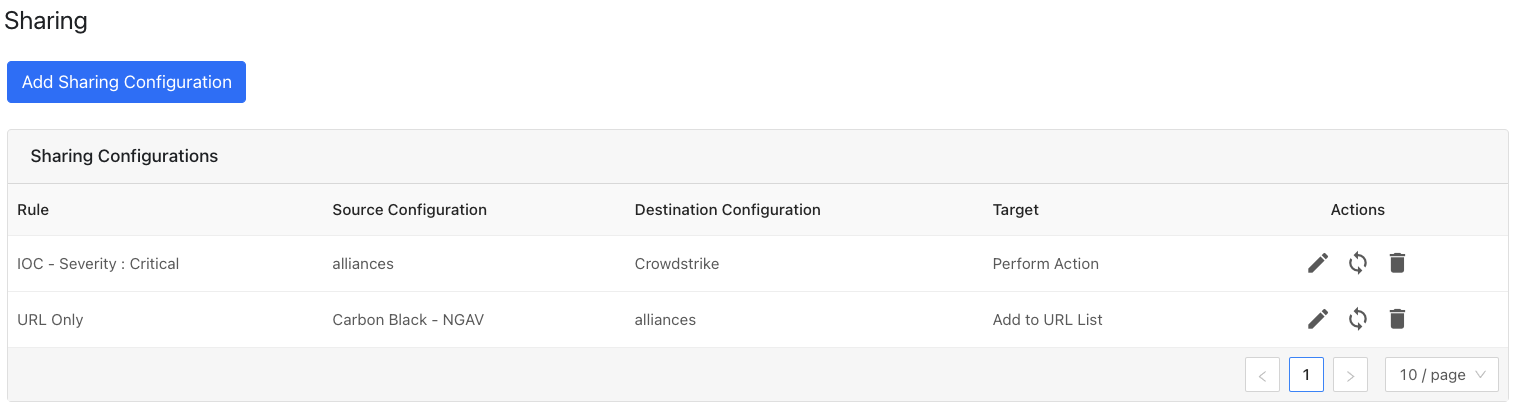 |
Edit the rule by clicking on the pencil icon.
Test the rule by clicking on the synchronization icon. This tests how many IoC will actually be sent to the destination system based on the timeframe and the rule.
Delete the rule by clicking on the garbage can icon.
In order to validate the integration you must have Netskope Alerts and/or MISP attributes/indicators. Polling Intervals was defined during plugin configuration. You can validate in both Netskope and MISP.
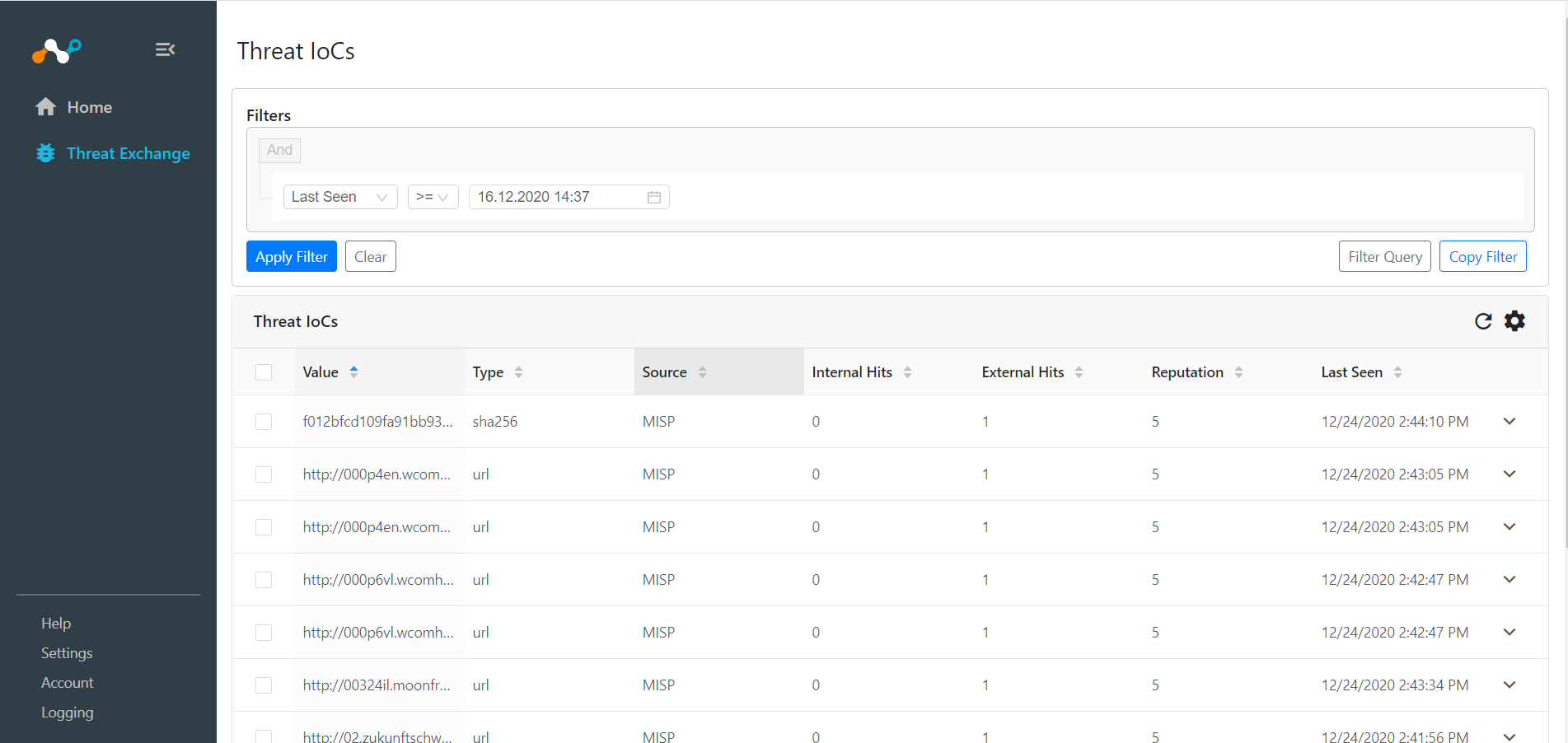
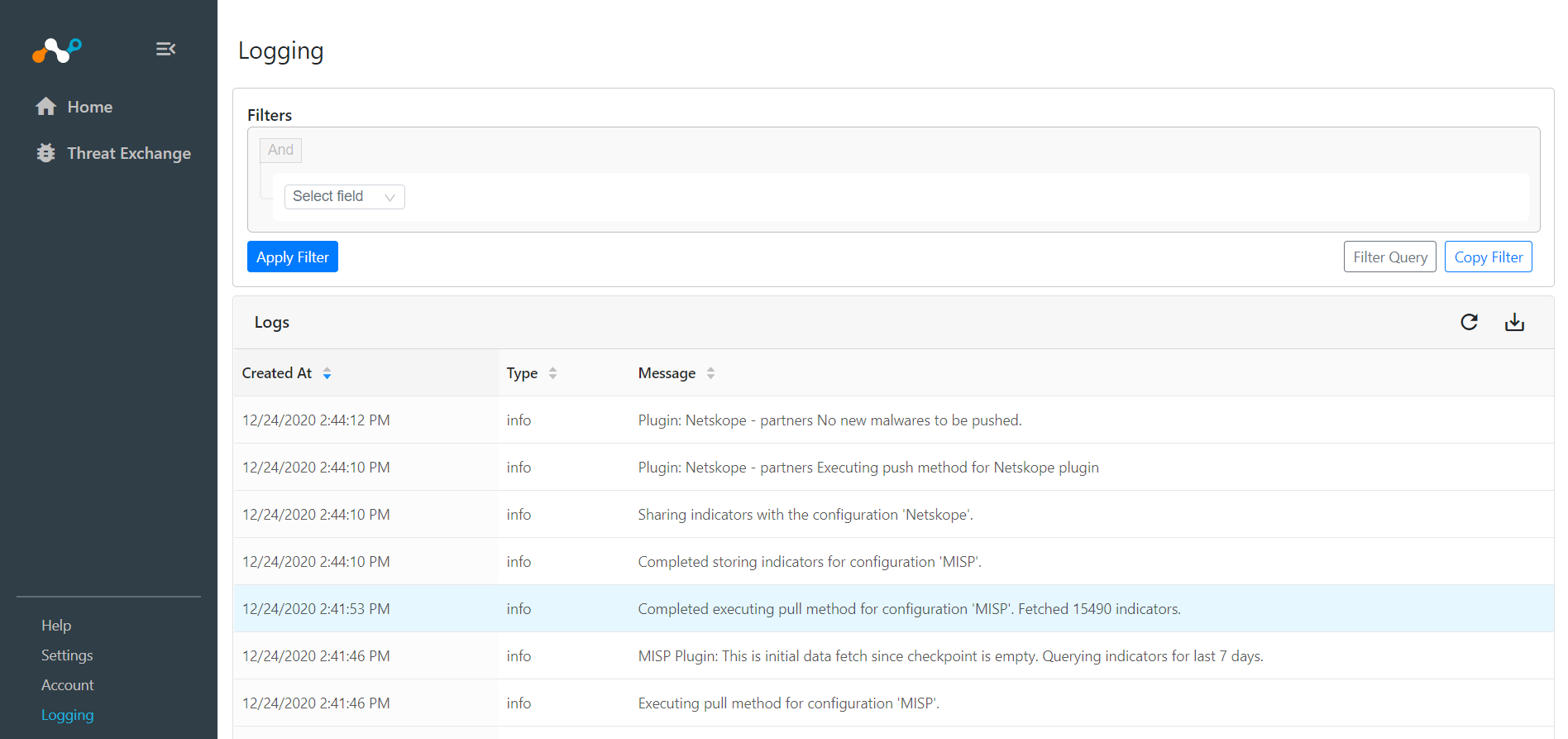
In Cloud Exchange, go to Threat Exchange, and click Threat IoCs. You should see records from your MISP plugin. You can filter based on Source values to check both the Netskope and MISP plugin.
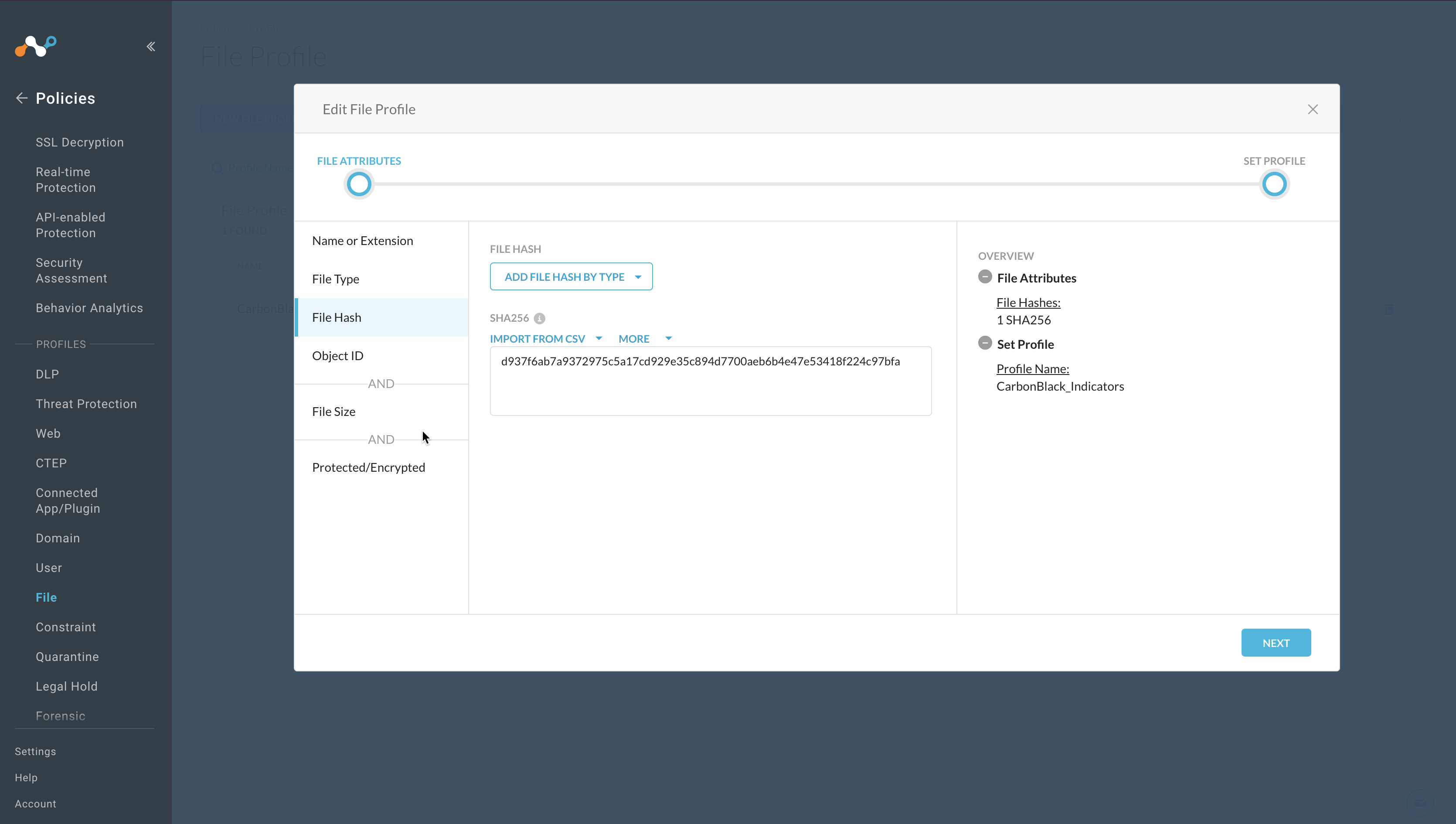
In the Netskope UI, go to Policies > File > Your Custom File Profile and click File Hash.
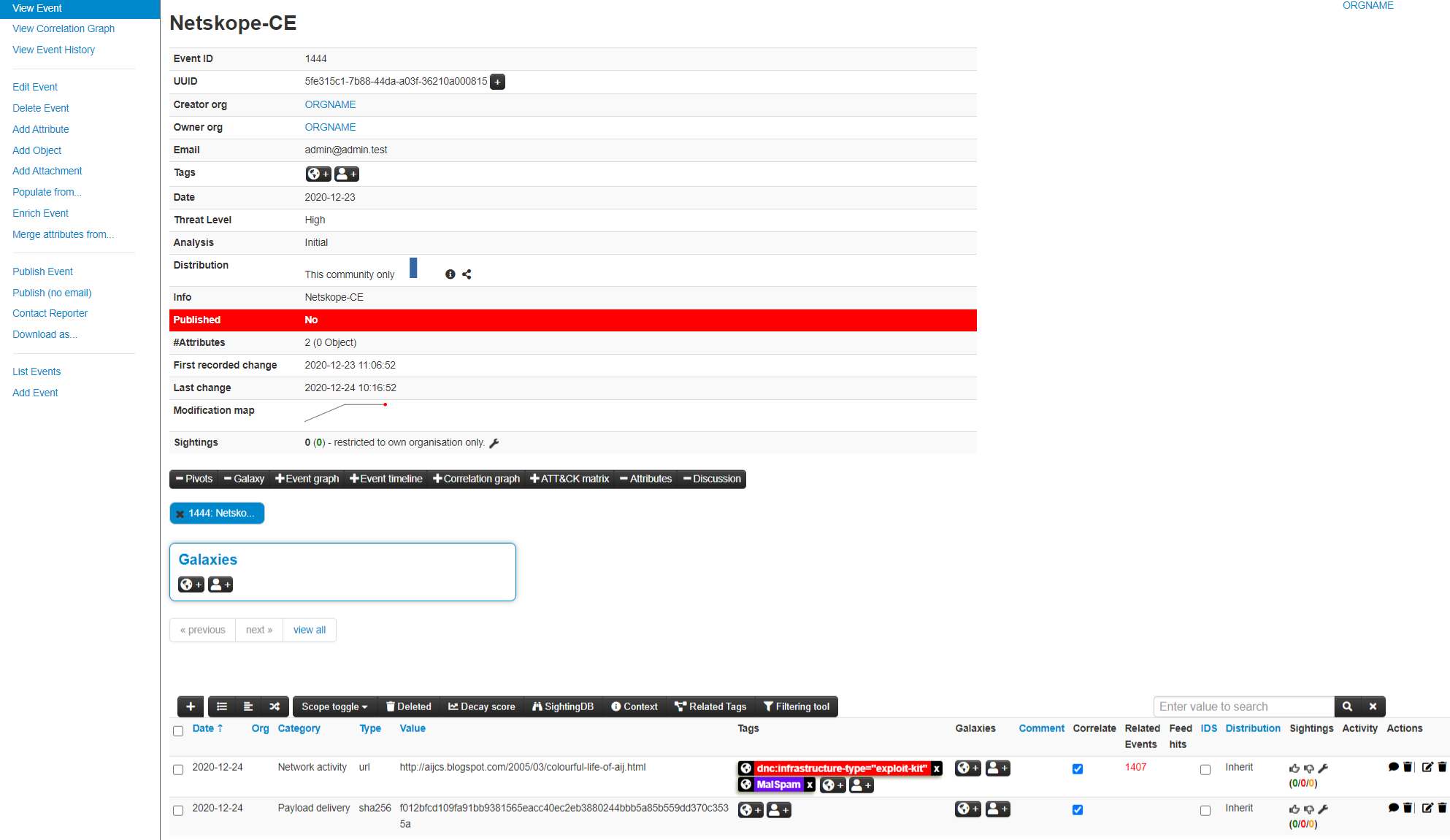
In the MISP Console, go to Event Actions > List Events and click the Id of the event having info same as value of your Event Name configuration parameter.
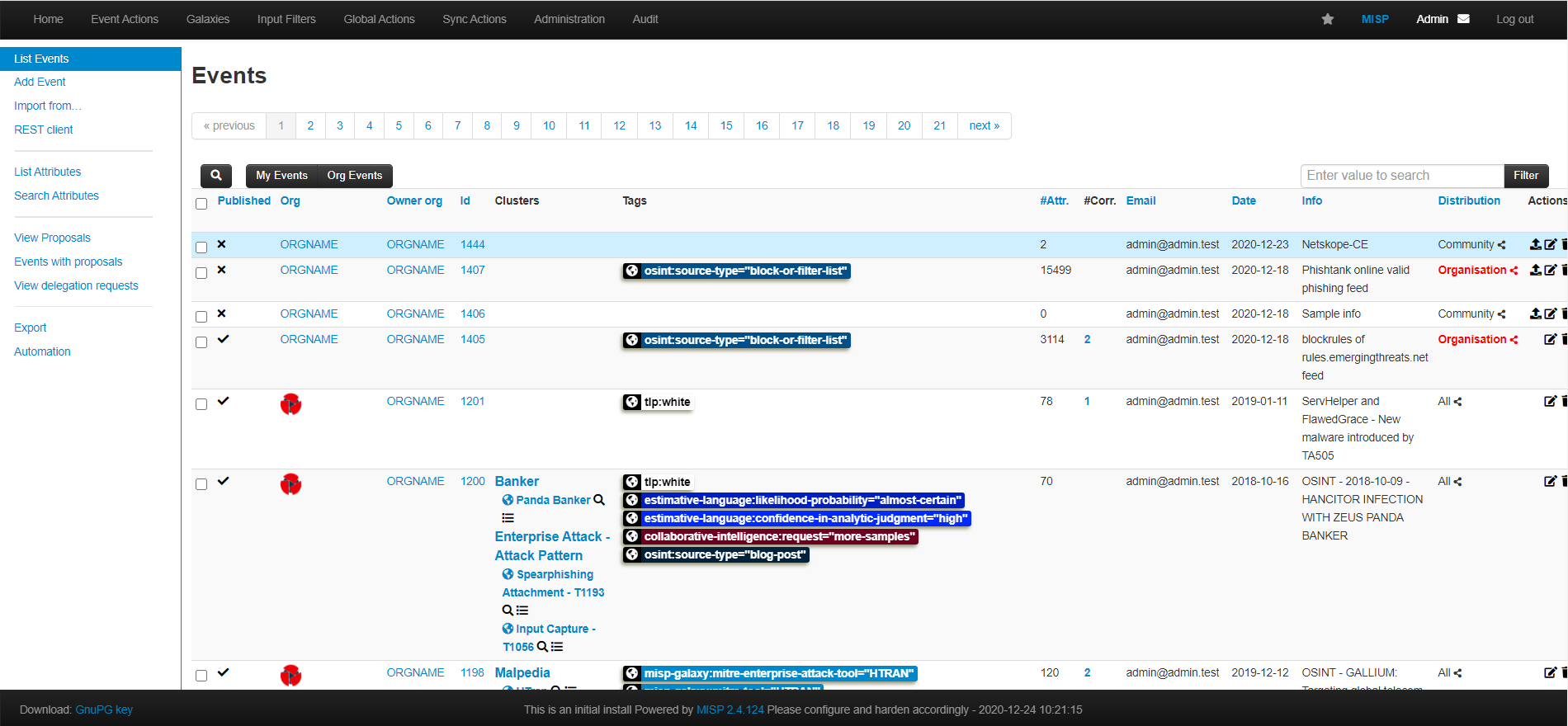
The event page will be displayed with the attached indicators as shown in the image below:
If data is not being brokered between the platforms, you can look at the Audit Logs in Cloud Exchange. In Cloud Exchange, go to Logging and ook through the logs for errors.
If while trying to upgrade a plugin you encounter the error shown here, then follow these steps:
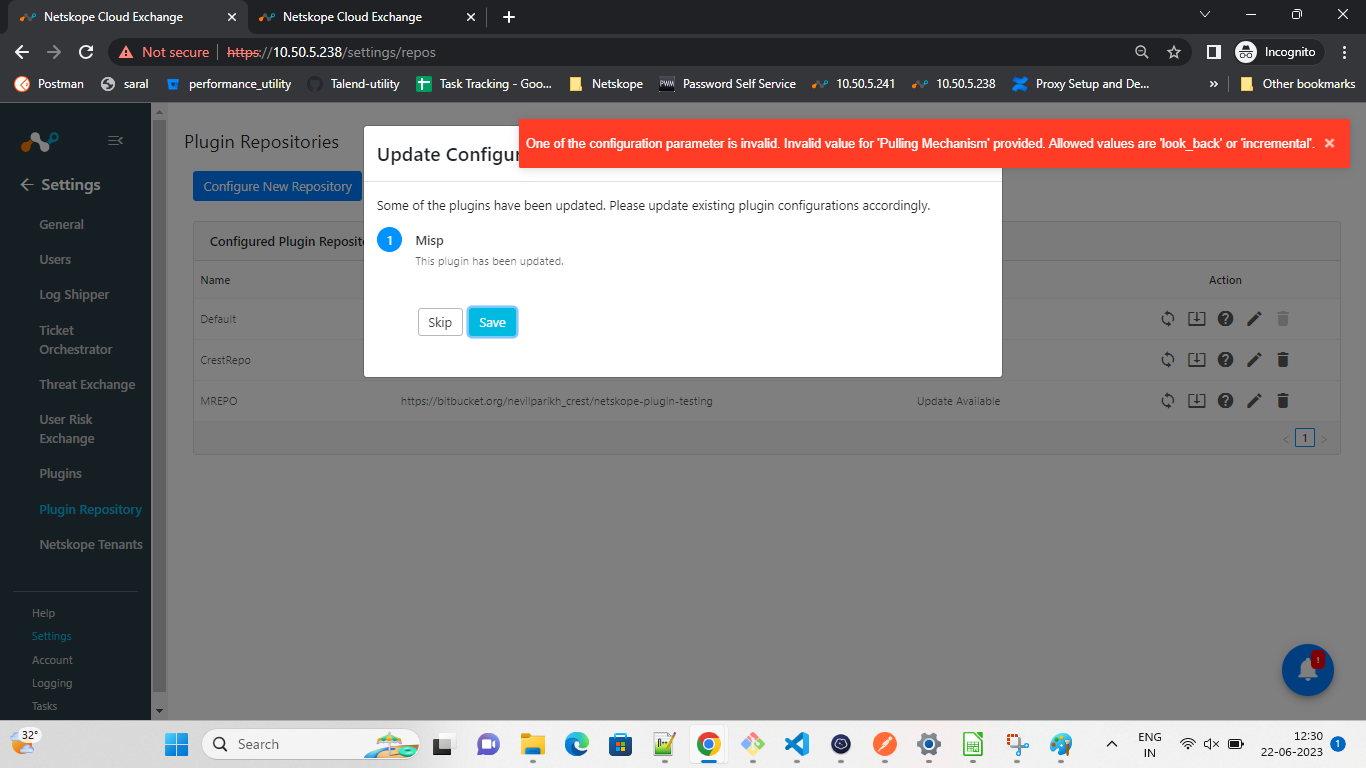 |
Click Skip.
Go to Threat Exchange > Plugins.
Edit the plugin as it will be disabled due to an error while upgrading the plugin.
Click Next.
Scroll down to newly added params (Pulling Mechanism and Look Back), and select the method of pulling and provided Look Back as per the Pulling Mechanism selected.
Click Save, and then enable the plugin.