Create a Real-time Protection Policy for Isolation (Targeted RBI)
Policies are defined using a set of variables. These variables define the criteria for detecting policy violations.
For descriptions for each of the variables used, refer to Real-time Protection Policy Variables.
Note
When you see a text box during the policy workflow, click in the text box to view your additional options or to edit your selection(s). These options dynamically display based on your initial template choice. Many criteria are set to ‘Any’ by default. This means the policy engine will not match against the criteria.
When available, click Add Criteria to see what other match criteria are supported. Add more criteria to your policy to make it more specific.
Optionally, click the 'X' to the far right of the text box to remove criteria.
To create a Targeted RBI Policy you need to take into account the following constraints and configurations for web pages to be isolated properly.
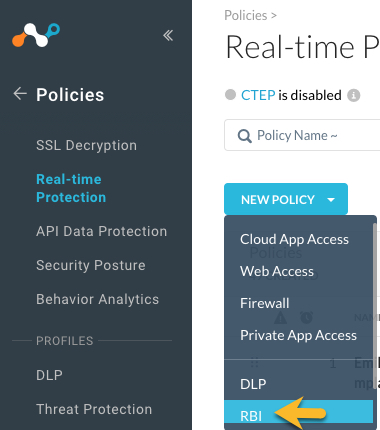
On the Real-time Protection Policies page, click New Policy > RBI. Your menu options may differ based on the licenses available for your account.
When you select RBI, the system automatically picks 'web access' and populates recommended fields, such as Category with the recommended RBI categories.
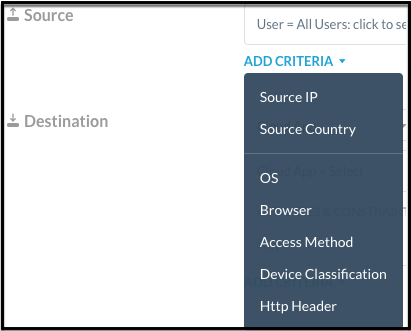
Select the Source. Click in the text box to select users. Traffic Criteria is sorted as 'Source' and 'Destination.' The system will show the most appropriate criteria based on your policy template selection. Many criteria are set to 'Any' by default. This means the policy engine will not match against the criteria.
Optionally, click Add Criteria to see what other match criteria are supported. Add more criteria to your policy to make it more specific.
For Destination, Category is automatically selected and it’s the only criteria that can be used for targeted RBI. You can choose to isolate any web page which falls in the following category list:
Newly Registered Domain
Newly Observed Domain
No Content
Parked Domains
Uncategorized
Web Proxies/Anonymizers.
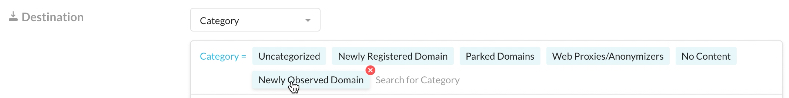
These categories are described in the RBI Category Definitions.
Tip
The system will notify you if you have added unrecommended categories to an isolation policy. Remove the unrecommended categories to avoid website performance degradation.
You can add more Destination criteria. The system will show the most appropriate criteria based on Application, Category, App Instance, or Private App selection. Leave this blank for RBI policies.
Select a Profile and Action. For RBI policies, select the "Isolate" action.
You can specify an RBI template. The default RBI template is applied but you can select a different template from the dropdown list.
Optionally, you can create a new template when the action is set to "Isolate" and attach it directly to the new Real-time Protection policy. Once created, it will be available in the list of RBI templates and admins can attach it to the RBI policy. To learn more: RBI Templates
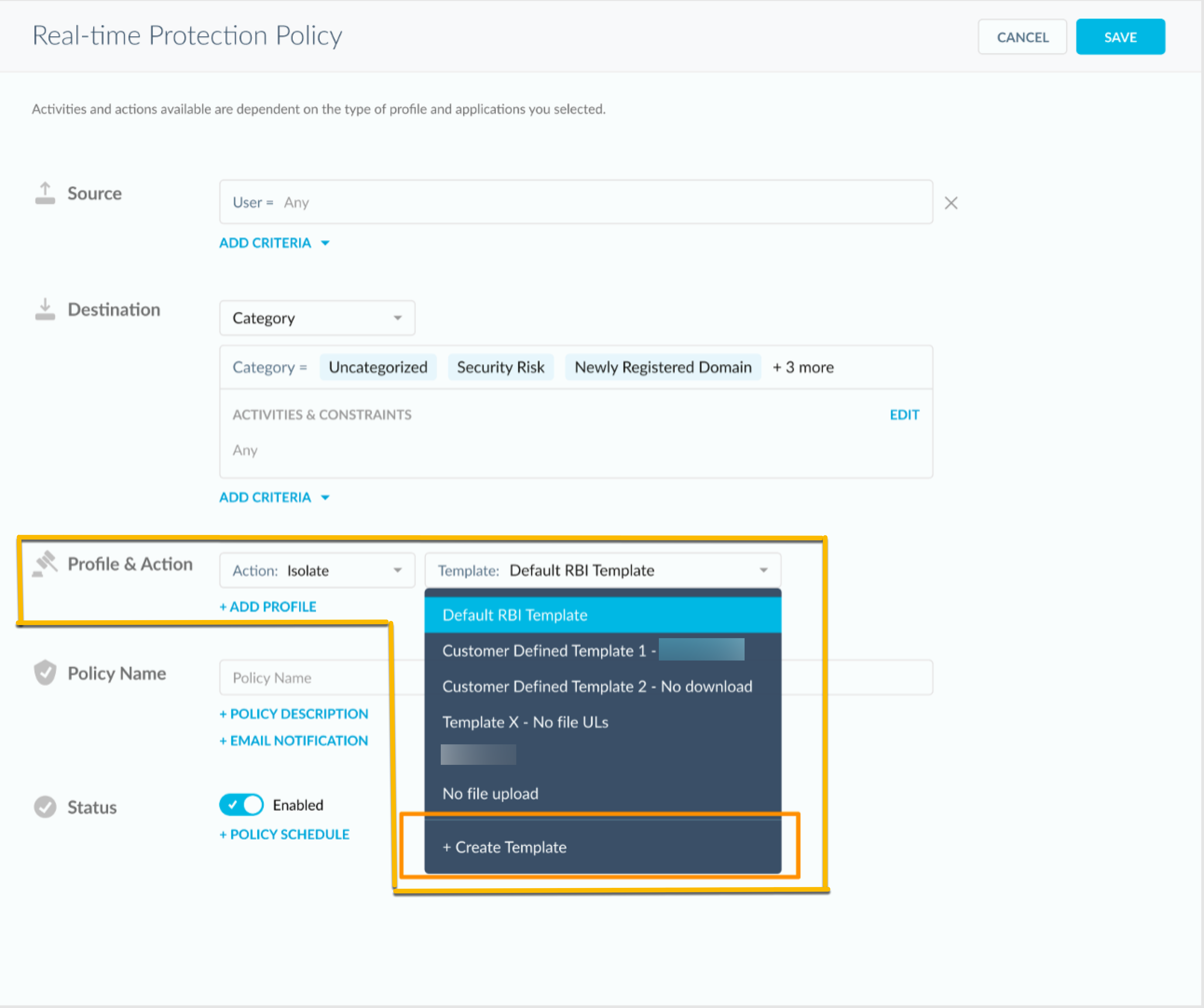
Do not add a DLP profile. They do not apply for targeted RBI.
Enter a name and a description.
Important
When creating policy names, only use alphanumeric characters and symbols such as "_" underscore, "-" dash, and "[ or ]" square brackets. You cannot use the greater than ">" and less than "<" symbols in policy names.
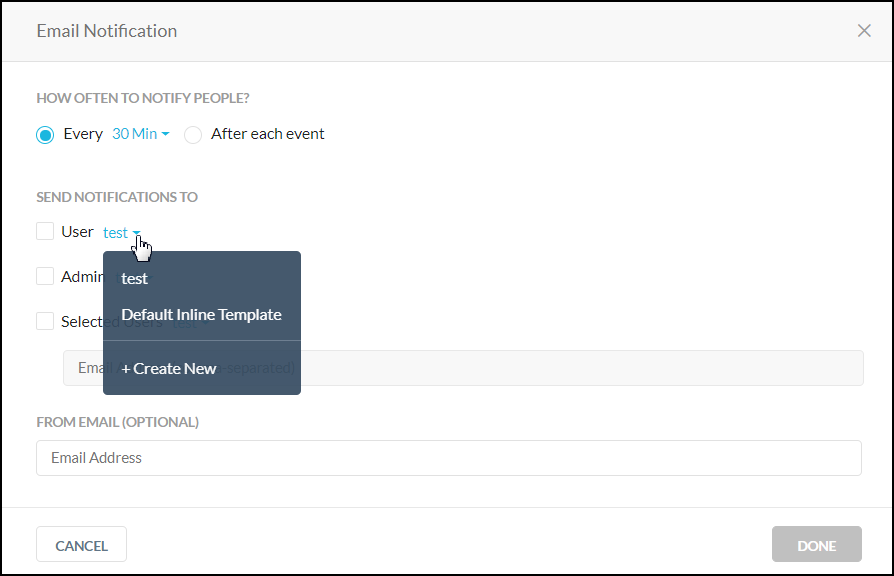
Select an Email Notification. Select the notification frequency. Choose None if you don't want an email notification about the policy violation and the resulting action. When you choose 'Every,' you can select the frequency of the email notifications from the dropdown list – 30 Mins, 60 Mins, 6 Hours, 24 Hours. Or, choose to notify 'After each event.'
Select the User, Admin, or Users to be notified. You can use the default email template or create a new template. Optionally, you can specify an email address that will appear as the sender in the email notification. When finished, click Done to save your email notification setting and exit the window.
Click Save in the upper right corner to save your new policy. You should see it in the Policy list page.
Tip
Navigate to Policies > Real-time Protection >
 > RBI Template to filter policies that are using a specific RBI template. Optionally, you can select Action > Isolate to view policies that are using the RBI Isolate action. To learn more: Isolation Events in Skope IT
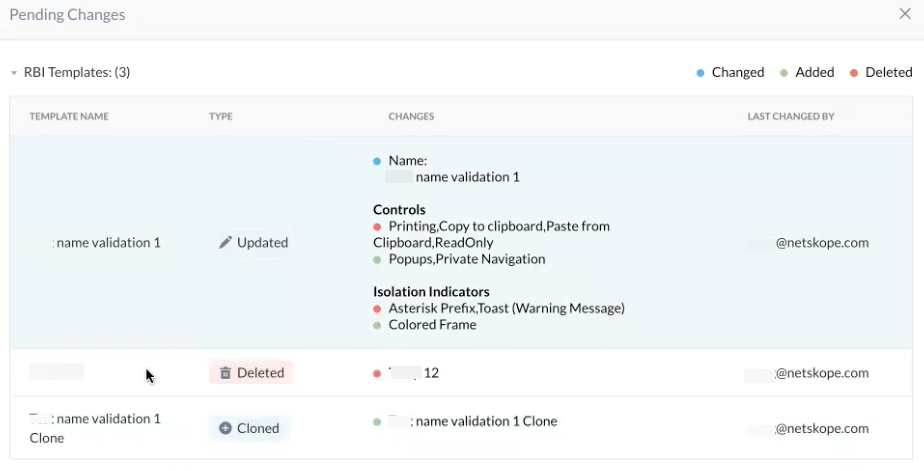
> RBI Template to filter policies that are using a specific RBI template. Optionally, you can select Action > Isolate to view policies that are using the RBI Isolate action. To learn more: Isolation Events in Skope ITOptionally, you can view pending changes for your RBI templates. Details such as field and controls that were edited, enabled, disabled, or cloned are described. Click Policies > Templates > RBI >

RBI Policy Variables
The following variables can be defined for an RBI Real-time Protection policy. You can use a variety of variables in a policy. If a variable is not used in the policy, it is defined as Any.
Variable | Description |
|---|---|
Users | Users created manually in the UI or Active directory users that are automatically populated from the enterprise AD server. |
User Groups | These are the Active Directory (AD) groups that are automatically populated to the Netskope cloud from the Enterprise AD server. Specifying user groups in a policy requires installing the Netskope AD adapter on a server that is part of your domain in order to export the AD user group names. |
Organizational Unit | This information is obtained from the exported AD groups. Specifying organizational units in a policy requires installing the Netskope AD adapter on a server that is part of your domain in order to export the AD organizational unit names. |
Cloud Apps + Web | Cloud app variables include:
|
Additional Attributes | These optional variables detect the following:
|
Action | Action taken when a violation is detected:
|
